Hidden in Plain Sight
Phasm hides encrypted messages inside ordinary photos.
No servers. No accounts. No trace.
What Is Steganography?
Encryption locks a message so no one can read it — but everyone can see the locked box. Steganography hides the message so no one knows it exists.
Phasm does both. Your message is encrypted and invisible, concealed inside a photo that looks completely normal. Send a vacation photo with a hidden note inside. Only the person with the passphrase can read it. Everyone else sees just a photo.
How It Works
1. Choose a Photo
Pick any JPEG photo — a selfie, a landscape, a meme. The more detail, the more text you can hide.
2. Type Your Message
Enter your secret text and an optional passphrase. Phasm encrypts and embeds it into the photo.
3. Share the Photo
Send the photo like any other. Only someone with the passphrase and Phasm can reveal the hidden message.
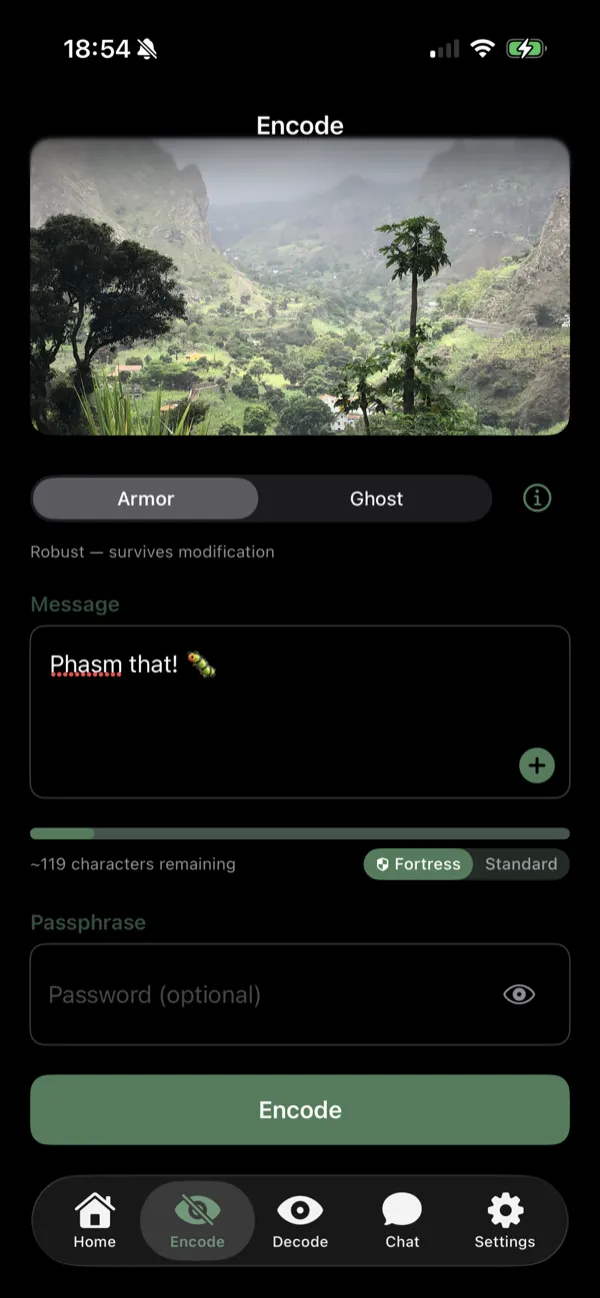
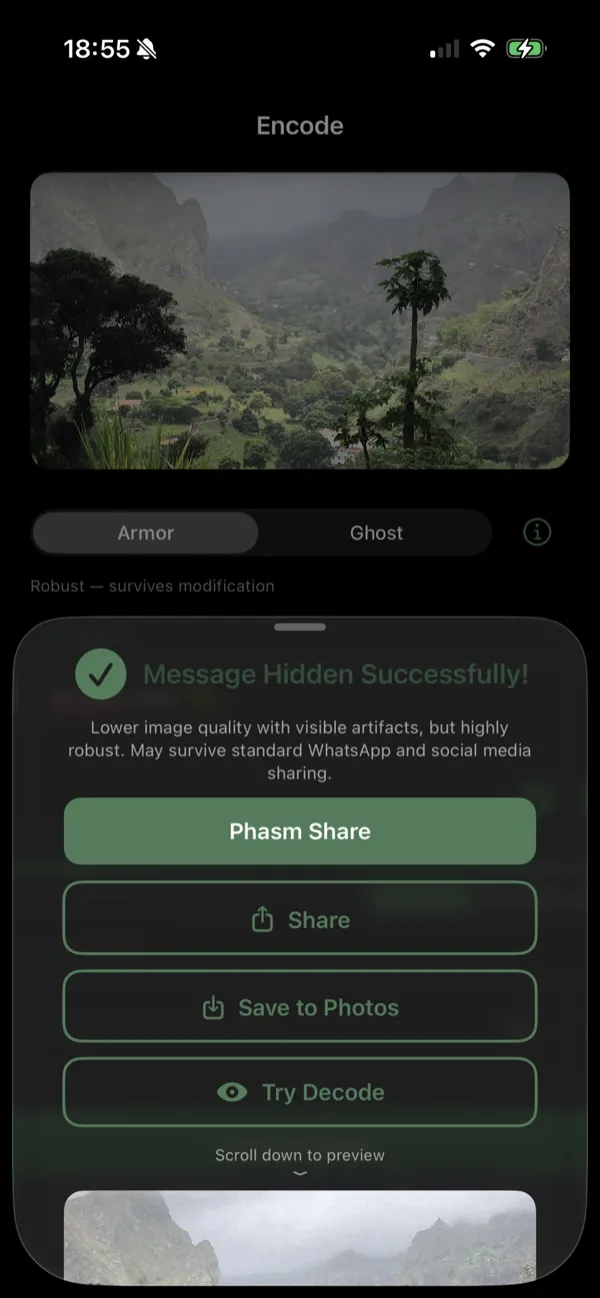
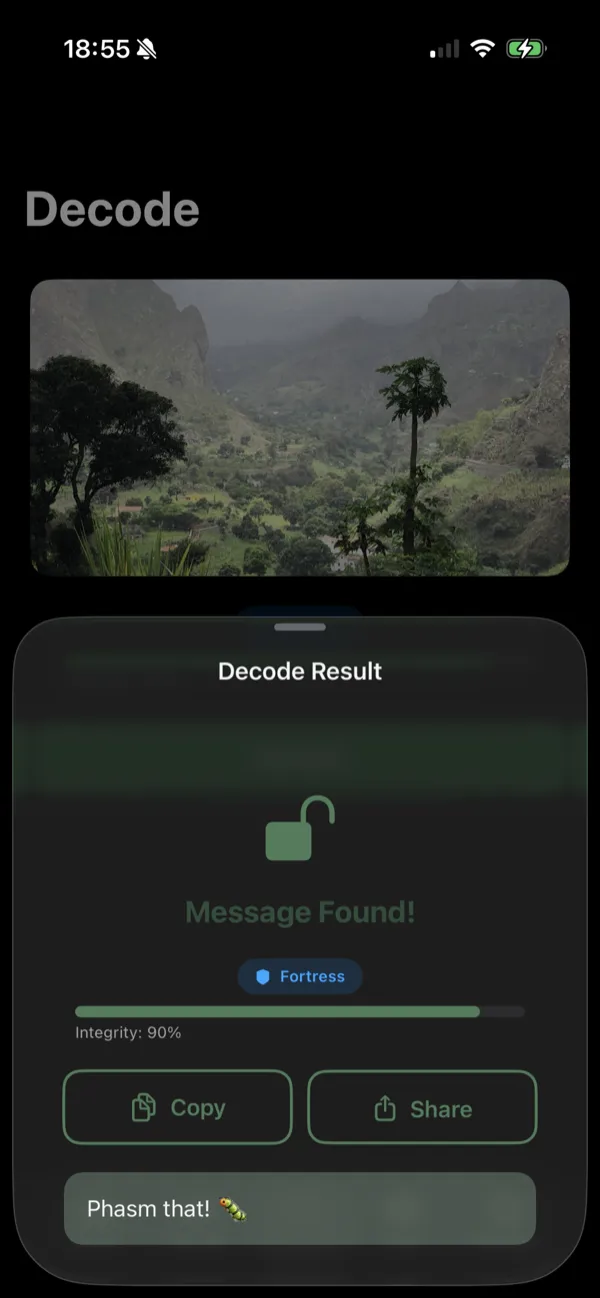
Encode a message, share the photo, decode on the other end.
Phasm Share — No App Needed to Decode
Your recipient doesn’t need the app. Upload your stego photo to phasm.link and get a short link you can send anywhere — text message, email, social media, QR code. The recipient opens the link and decodes the hidden message directly in their browser.
Browser Decode
The landing page runs the same Rust engine compiled to WebAssembly. No plugins, no downloads — just open the link.
iOS App Clip
On iPhone, tapping a phasm.link URL opens an instant decode experience. No App Store visit, no install, no waiting.
Privacy First
Uploaded photos are stripped of EXIF metadata and expire automatically. The server never sees your passphrase or message — decryption happens on the recipient’s device.
Already have the app? phasm.link URLs open directly in Phasm on both iOS and Android via Universal Links and Deep Links.
Three Modes
Different situations need different approaches. Phasm gives you three.
Ghost Mode — Invisible
Optimized for stealth. Uses adaptive steganographic algorithms from published academic research to resist forensic detection. Even machine-learning steganalysis tools cannot find the hidden message.
Use when the photo might be analyzed by someone looking for hidden data.
Armor Mode — Indestructible
Optimized for durability. Error-correcting codes let hidden messages survive JPEG recompression, light cropping, and platform processing.
Use when the photo will be forwarded, downloaded, or shared across platforms.
Fortress Mode — Unstoppable
Activates automatically for short messages in Armor mode. Aggressive repetition coding survives even WhatsApp standard recompression — a channel that defeats most steganographic methods.
Use for short, critical messages that must survive any platform.
How Ghost mode resists detection → How Armor mode survives recompression →
Who Uses Phasm?


Just for Fun
Hide a secret note in a group photo and see who finds it first. Embed a birthday message inside a selfie. Send your friend a meme with a hidden punchline. Run a scavenger hunt with clues hidden in photos. Share your Wi-Fi password inside the photo hanging on your fridge.
Most Phasm users are here for the fun of it. No expertise required.
The Curious Tinkerer
“Wait, you can actually hide text inside a JPEG?” Yes. Open the tool, try it yourself. It takes 30 seconds.
Privacy-Conscious Communicators
When encrypted messaging apps draw suspicion, a photo draws none. Phasm adds a layer of deniability that encryption alone cannot provide.
Journalists & Activists
Send a photo from a country where encrypted apps are monitored. The message travels inside an ordinary-looking image.
Security Researchers
Test steganographic embedding and detection techniques on real-world images. Phasm implements published algorithms you can verify — the core engine (phasmcore) is open source on GitHub for full code review.
Why Phasm?
Zero Servers
Everything happens on your device. There is no server to hack, subpoena, or breach.
Always Encrypted
AES-256-GCM-SIV encryption is not optional. Every message is encrypted before embedding.
Academic Foundations
Built on peer-reviewed algorithms from steganography research. STC, STDM, Reed-Solomon, Watson masking. The core engine is open source.
Pure Rust
One codebase compiled to iOS, Android, and WebAssembly. No C dependencies.
Free, No Account
No sign-up, no tracking, no ads. Open the tool and use it.
37 Languages
Error messages and UI strings localized globally. Use Phasm in your language.
Security Details
Phasm is built for people who care about the details. Here is what is under the hood.
Encryption
Every message is encrypted with AES-256-GCM-SIV authenticated encryption. When you set a passphrase, it is strengthened using Argon2id key derivation (memory-hard, resistant to GPU/ASIC attacks). All key-derived randomness uses the ChaCha20 stream cipher as PRNG.
Messages without a user passphrase are still encrypted with a default key — the data is never stored in plaintext inside the image.
Ghost Mode
Uses adaptive steganographic cost functions from published academic research to identify which DCT coefficients can be modified with minimal statistical footprint. Changes are applied using Syndrome-Trellis Coding (STC), which minimizes the total distortion for a given payload. At Phasm’s low embedding rates (~0.02–0.04 bpnzAC), detection accuracy approaches random chance even with state-of-the-art deep-learning classifiers.
Armor Mode
Uses Spread Transform Dither Modulation (STDM) for quantization-based embedding that survives re-quantization. Reed-Solomon error correction recovers from bit errors caused by recompression. Coefficient stability selection and block interleaving further improve robustness. Watson perceptual masking adapts the embedding strength per-block based on visual sensitivity.
Armor’s Fortress sub-mode activates automatically for short messages, using aggressive repetition coding to survive even WhatsApp standard recompression.
What Phasm Does NOT Do
We believe in honesty about limitations:
- Phasm is not a general-purpose encryption tool — it is steganography
- Payload is short text only (up to ~64KB depending on image size)
- Instagram, Snapchat, and WeChat destroy hidden messages (they resize images aggressively)
- No security tool is magic — operational security matters too
Why “Phasm”?
The name comes from phasmid — stick insects and leaf insects, the masters of hiding in plain sight. The word itself derives from the Greek phasma, meaning phantom or ghost.
A phasmid doesn’t run or fight. It hides by becoming indistinguishable from its surroundings. Steganography works the same way — your message becomes indistinguishable from an ordinary photo.

Frequently Asked Questions
Can law enforcement break this?
The encryption is AES-256-GCM-SIV with Argon2id key derivation — the same standard used by Signal, WhatsApp, and government systems. Ghost mode’s steganographic embedding resists detection at near-random-chance accuracy. The core engine is open source, so you do not have to take our word for it — anyone can audit the code. That said, no security tool is magic. Operational security (who you share the passphrase with, how you hide the app) matters too.
What if I forget my passphrase?
Messages encoded with a passphrase cannot be recovered without it. This is by design — there is no “forgot password” option because there is no server storing your data. Messages without a passphrase can be decoded by anyone with Phasm.
Does it work on social media?
It depends on the platform. Direct sharing (AirDrop, email, messaging as a file) always works. Some platforms like Telegram and Twitter/X preserve the hidden data under certain conditions. Instagram, Snapchat, and WeChat resize images aggressively and destroy hidden messages.
Can my friend decode without installing the app?
Yes. Share via phasm.link and the recipient decodes directly in their browser. On iOS, the App Clip provides an instant decode experience with zero install.
Is it really free?
Yes. No premium tier, no ads, no in-app purchases. Phasm is an independent project, not a venture-funded startup looking for an exit.
Is it open source?
Yes. The core steganography engine (phasmcore) is open source under the GPL-3.0 license on GitHub. You can review the Rust source code for the encryption, embedding algorithms, and everything that touches your data.
Try Phasm
Hide a secret message in any JPEG photo. No account needed, no data leaves your device.